With the FDA and other regulatory bodies focusing on cybersecurity in medical devices, this technical white paper comes at an important time. Clarius’ ultrasound systems are not only handheld and high-performance, but also have the benefit of running on most mobile devices and integrating with Cloud services. These were designed and engineered through security-driven requirements from the beginning.
I’m continually impressed to see the level of security that has gone into developing each component in the system, from the Clarius App to Clarius Cloud, and even the ultrasound device itself. It really makes my job a lot easier,” says Luis Araujo, Manager, Information Security. “I wasn’t here in the beginning, but as I develop procedures and gather information, I always run into design documents from a few years ago, when the product was still in a concept-phase, that outline security mechanisms and build them into the architecture from the ground up. Because of this early focus, we have no problems meeting HIPAA, HITRUST, and GDPR requirements. It seems rare in any industry, let alone the medical industry.”
Since there are many types of users that want to have access to portable ultrasound technology, Clarius also offers a complete DICOM-based workflow solution, where users can choose to store and manage data on their existing PACS systems, and essentially bypass the Clarius Cloud solution.
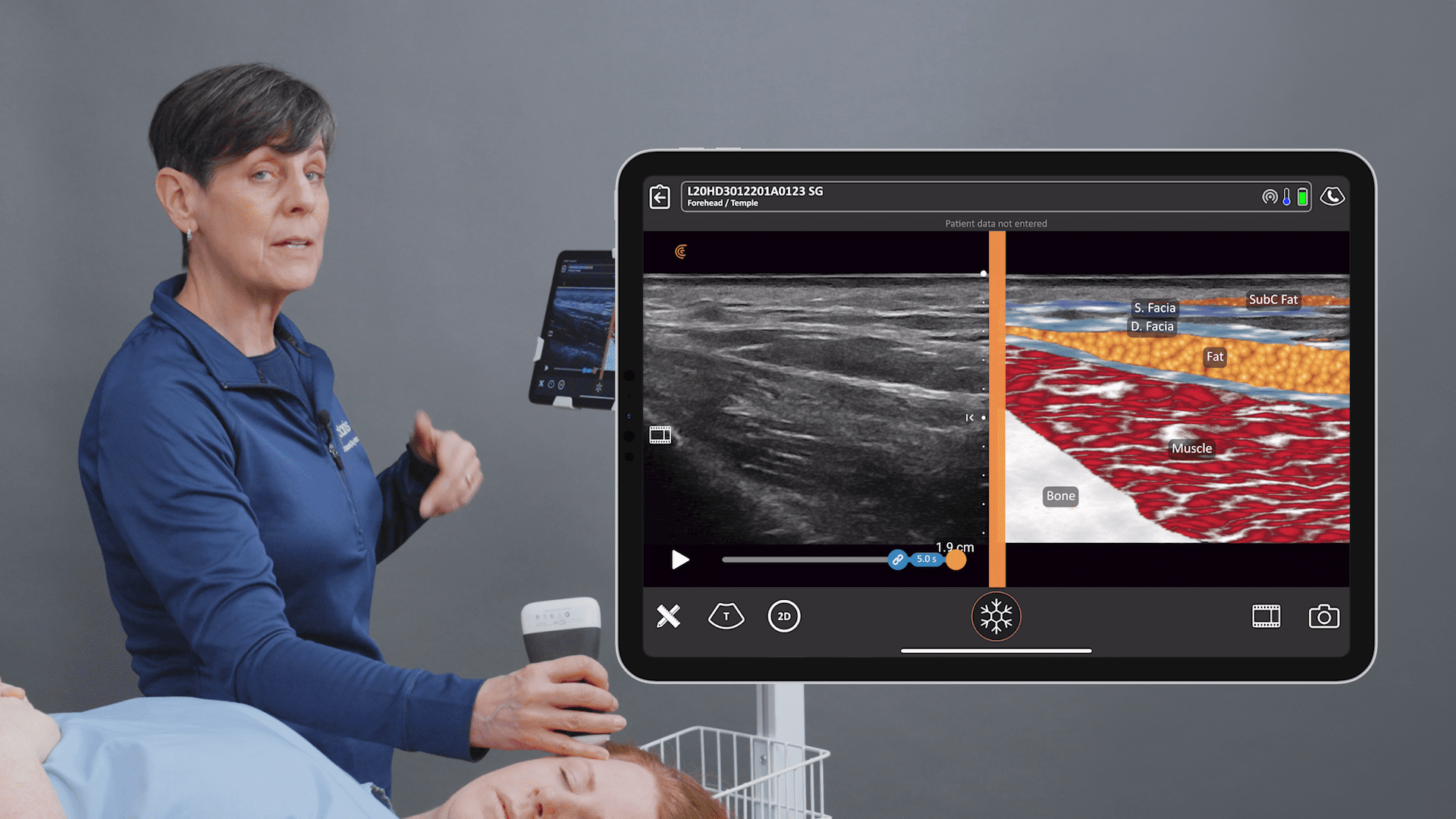
We want to make it easy for users to manage and access their data, as well as deploy their equipment,” says Laurent Pelissier, CEO. “For hospitals, an IT department can easily and securely manage and use the Clarius App, as well as do a simple one-time PACS configuration that synchronizes with all Clarius equipment within their system. For private clinics and doctors who value premium portability, Clarius Cloud is an excellent and easy to use solution for data management, with features that no other ultrasound vendor currently provides.”
Information security is a broad topic, and the paper also covers important details such as:
- Wi-Fi and Bluetooth security
- App security measures
- Cloud infrastructure and associated compliance and operational controls
- DICOM workflows
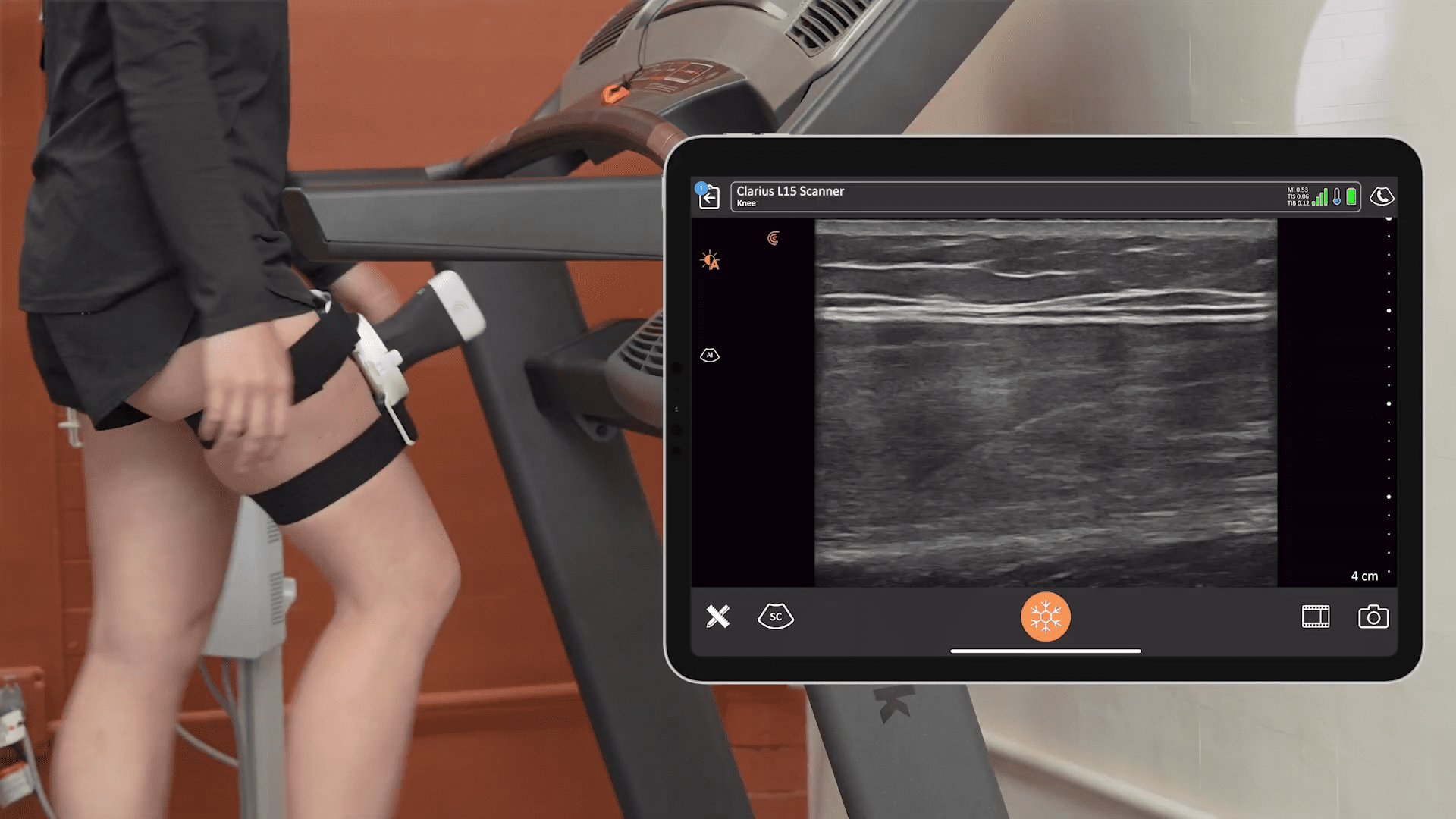
Clarius Cloud and DICOM capabilities are available on all three Clarius scanner models. The Clarius App can be downloaded on iOS and Android smart devices.
Read the full paper: Information Security